ChainThink
Stay ahead, master crypto insights
How did XPL attackers exploit Hyperliquid's rules, giving all DEXs a lesson worth millions of dollars?
How did XPL attackers exploit Hyperliquid's rules, giving all DEXs a lesson worth millions of dollars?

2025-08-29 12:17
Author: Carrot
This is not a hack, it's a strategy
Two days ago, a textbook-level "precise sniper" attack took place on Hyperliquid, with the token $XPL as the main target. In the end, the attacker used less than $200,000 in costs to trigger a large-scale short liquidation, making over $10 million.
The key point is:This was not a hacking attack, and the attacker did not exploit any code vulnerabilities.
Instead, he utilized the DEX's most proud feature — complete transparency. This was a hunt conducted in the open, fully compliant with protocol rules. This incident is like a mirror, reflecting the structural weaknesses under the glossy surface of all on-chain exchanges (DEX).
Part One: The Three-Step Attack - How the Hunt Happened?
To understand this attack, you need to know a core mechanism of perpetual contract exchanges:Price Feed. Simply put, the contract platform needs a "real price" to determine who is winning, who is losing, and who should be forcibly liquidated. This "real price" usually comes from external sources, such as on-chain spot markets.
The attacker's script revolved around this "price feed" mechanism in three steps:
Step One: Finding the Perfect Prey
The attacker found $XPL. The perfection of this token lies in that its perpetual contracts had trading volume on Hyperliquid, but its spot market was almost entirely concentrated on a small exchange called Zebra on the Arbitrum chain, with extremely shallow liquidity. This meant that only a small amount of money could push the spot price to the sky.
Step Two: Polluting the Price Source
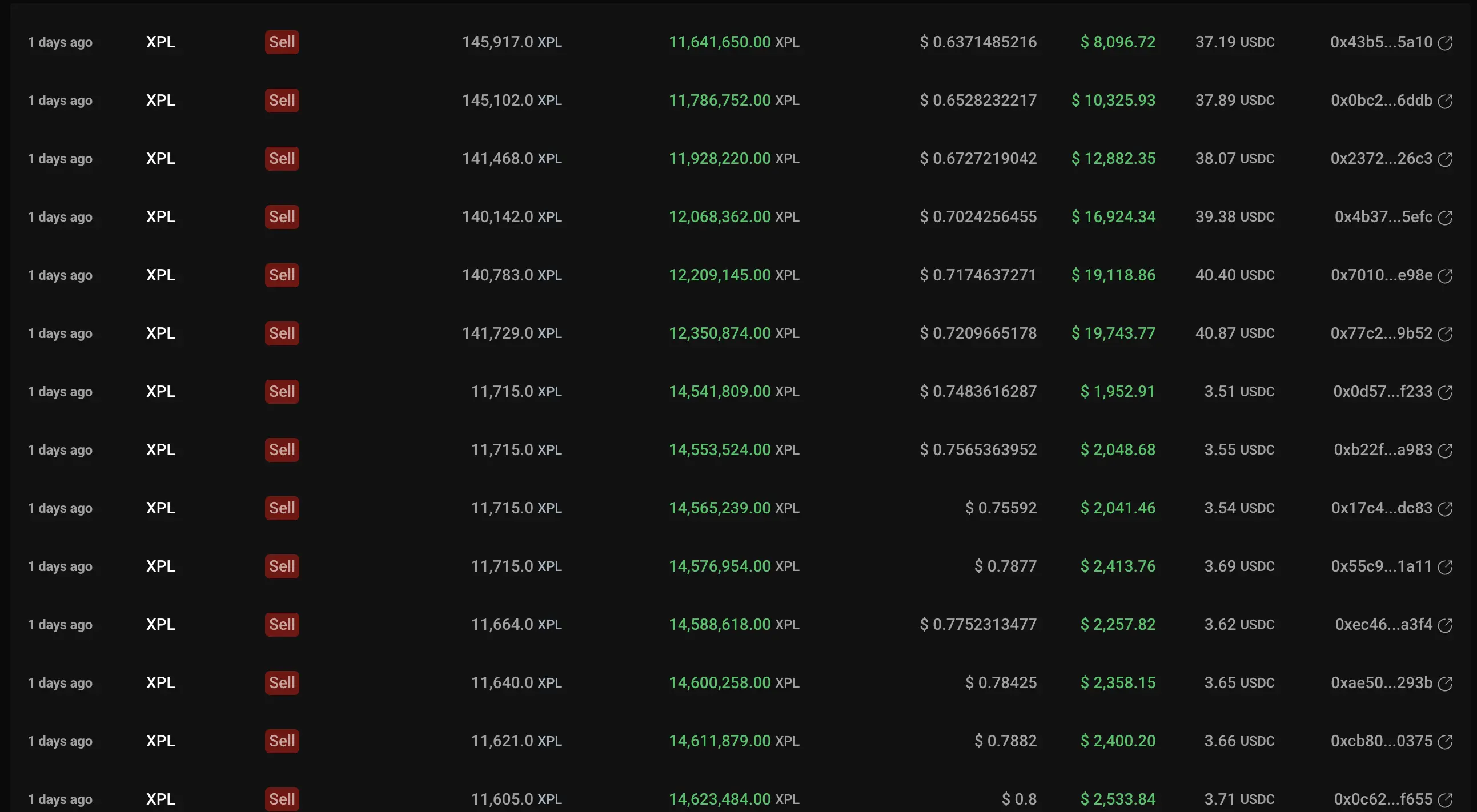
According to on-chain data, the attacker bought a large amount of XPL spot on Zebra using approximately $184,000 in WETH. The result was immediate, with the spot price being pushed up nearly eight times within a short period. Hyperliquid's price feed mechanism referenced this spot price, thus successfully polluting the "real price" in the contract, artificially pushing it to an absurd height.
Step Three: Harvesting the Short Sellers
When the contract price soared abnormally, all short positions were forced to face liquidation. On a platform like Hyperliquid, where the order book is completely transparent, who will be liquidated at which price is almost a semi-public secret. The attacker looked at this "liquidation map" and precisely pushed the price past the trigger point. A large number of shorts were forcibly liquidated, while the attackers, who had already been waiting, easily took over these blood-stained chips,making a profit of about $15 million.

Part Two: Is the 'Full Transparency' of DEX a Virtue or a Curse?
This incident raises a soul-searching question: Is the transparency that DEXs pride themselves on a good thing, or a curse?
It is a sharp double-edged sword.
For ordinary users, transparency means fairness, verifiability, and no backdoor operations. But for attackers, a transparent order book is an attack map, and automated smart contracts are an executioner.
The protocol is neutral, it cannot distinguish between good and evil. As long as you play by the rules, it will faithfully execute. This "absolute neutrality" becomes a cash machine for whales in low liquidity markets. That is why, in the face of such naked attacks, the protocol itself is powerless.
Part Three: Is It Safe to Return to CEX?
Since DEX is so dangerous, what if we return to the embrace of CEX?
CEX does have its "firewall." Strict KYC, internal risk control teams, and price limit mechanisms can effectively increase the difficulty of such attacks. It would be almost impossible to manipulate the contract price of a coin on Binance with $200,000.
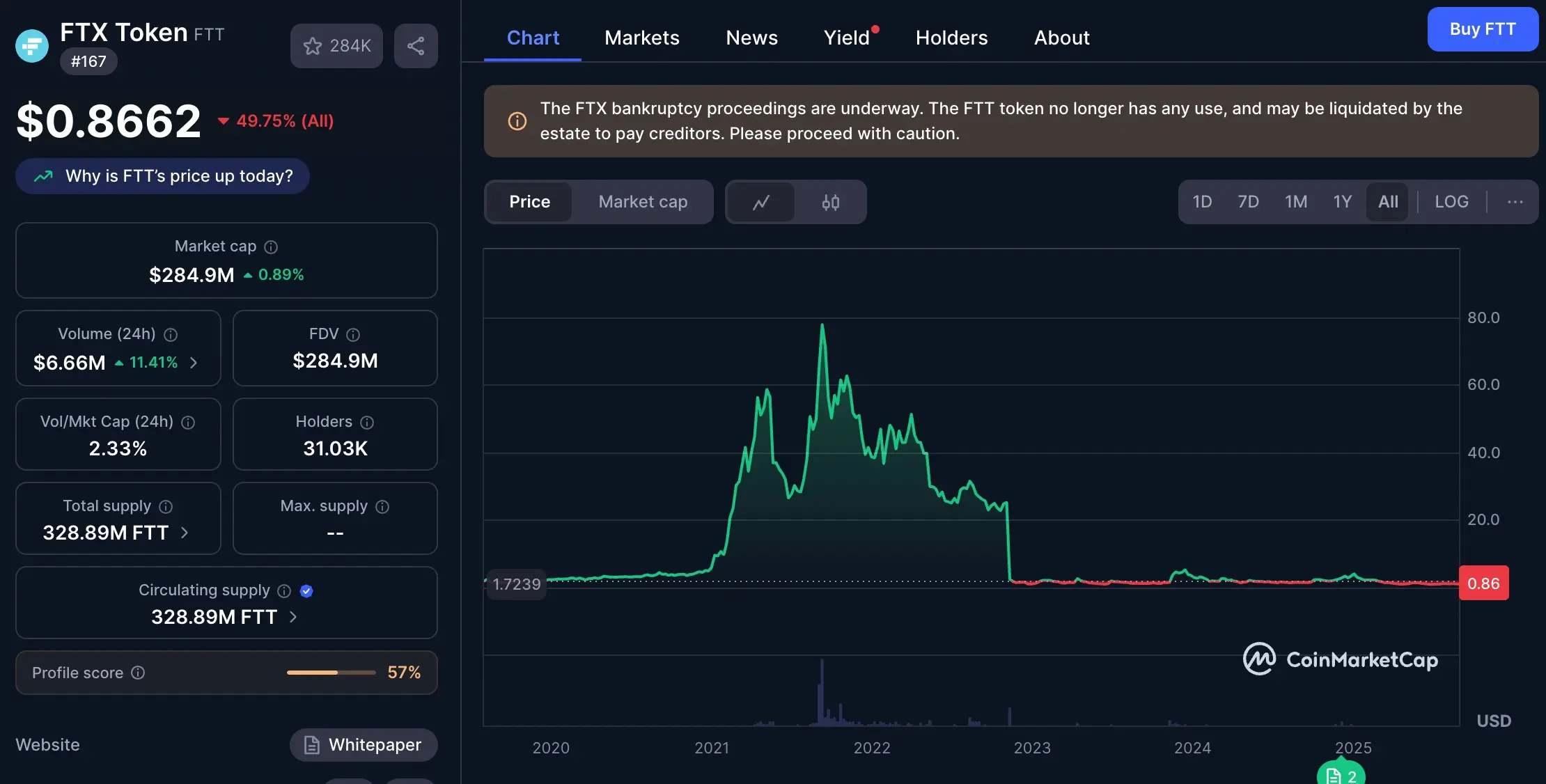
But is that safe? No. CEX just transforms "visible evil" into "invisible evil."
On DEX, the rules are public, and the risks are calculable. On CEX, you face a black box. Your biggest risk is no longer an external sniper, but the exchange itself. The story of FTX and Alameda Research is the best proof — when embezzlement occurs, you will know nothing until everything is zero.
So, the key issue has never been which is better between DEX and CEX, but how to learn from both and create a more evolved species.
Part Four: Seeking Answers from the Architecture - Taking QuBitDEX as an Example
The $XPL event tells us that simply moving transactions onto the blockchain is far from enough. The future of the industry must address these fundamental issues from an architectural perspective.
First, the price feed mechanism must evolve. A single, low-liquidity spot market must not become the sole basis for determining the fate of tens of millions of dollars in positions. For example, one of the core principles QuBitDEX has explored and established since its design is to aggregate depth data streams from multiple leading CEXs and combine them with a time-weighted average price (TWAP) mechanism, fundamentally increasing the cost of price pollution exponentially.
Second, absolute transparency needs to be rethought. Is there a possibility that we can ensure the verifiability of settlement while protecting the privacy of traders' strategies? This is also the direction QuBitDEX is exploring through its native Layer-1 ZK compatibility. Trading models like on-chain dark pools can effectively prevent malicious sniping without sacrificing the decentralized trust foundation.
Finally, the protocol itself must become "smarter." It needs to have native risk management capabilities, rather than just being a passive executor. In the architecture described in QuBitDEX's whitepaper, its native AI layer is designed as a real-time risk engine, capable of dynamically analyzing the market, identifying abnormal trading patterns, and providing a basis for protocol-level risk control. This approach of embedding risk management into the protocol's DNA represents an important evolution direction for DEX architecture.
Final Conclusion
The XPL event gave everyone a $10 million lesson: the next generation of DEXs can no longer be simple replicas of the blockchain. The future of the industry belongs to protocols that deeply understand and solve these structural weaknesses.
True innovation comes from platforms that can deeply synthesize the mature risk control concepts of CEXs with the verifiable, decentralized spirit of DEXs.
Disclaimer: Contains third-party opinions, does not constitute financial advice







AI Practical Guide
This column focuses on the real progress of Agents: technological evolution, application implementat
Crypto Weekly
Tracking on-chain movements of the smart money and institutions
Frontier Insights
Spotlight on Frontier, trending projects, and breaking events
Blowup Alert
As the 2026 crypto bear market deepens, exit scams and project blowups are becoming increasingly fre
Regulatory Watch
American Crypto Act – timely interpretations of policies worldwide
Popular Airdrop Tutorial
Selected potential airdrop opportunities to gain big with small investments
FusnChain
FusnChain
